Anthropic Accidentally Shipped Their Source Code: What Actually Happened
You've probably seen the memes. "Anthropic lost all their source code!" "TypeScript destroyed an AI company!" Here's what actually happened, why it matters, and how you can check if you're making the same mistake.
What Actually Happened
Anthropic dropped a new release on us — they didn't "lose" their source code. They accidentally published it.
When they released Claude Code as an npm package, someone forgot to exclude a .map file from the build. That file was a TypeScript source map — a 59.8 MB file included in version 2.1.88 of @anthropic-ai/claude-code. It contained everything needed to reconstruct the original source code.
The result: ~512,000 lines across ~1,900 files of Claude Code's internal TypeScript codebase became public.
No customer data. No credentials. No model weights. Just the code behind Claude Code itself.
Anthropic confirmed it was human error in the release process, not a hack. Then Chaofan Shou (@Fried_rice) dropped this tweet on us while interning at Solayer Labs.
This was the second time Anthropic leaked Claude Code source via source maps. A similar incident was reported to have happened with an earlier version in February 2025.
What's a Source Map?
When you view a page that uses JavaScript, your browser has to be able to read the code to execute it — and you can view it the same way the browser does. To make it harder to read, developers minify and bundle their code, stripping whitespace and renaming variables into an unreadable mess.
Source maps reverse that process. They're debugging files that map compiled/minified code back to the original source. Essential for development, but they should never ship to production.
Think of it like a bank vault blueprint. Minified code is the steel door — it makes it hard to see what's inside. A source map is the blueprint showing every room, every lock combination, and where the money is. Leaving it on a public server is like pinning the blueprint to the front door.
Pick your speed:
The Internet Had a Field Day
The memes were immediate.
But the most interesting fallout wasn't memes — it was what people built.
The Code Goes Viral
claw-code: The Clean-Room Rewrite
claw-code — a clean-room Rust rewrite inspired by the leaked architecture. It wasn't a copy of the TypeScript source; it was a from-scratch implementation based on understanding how Claude Code works under the hood.
It became one of the fastest-growing repos in GitHub history:
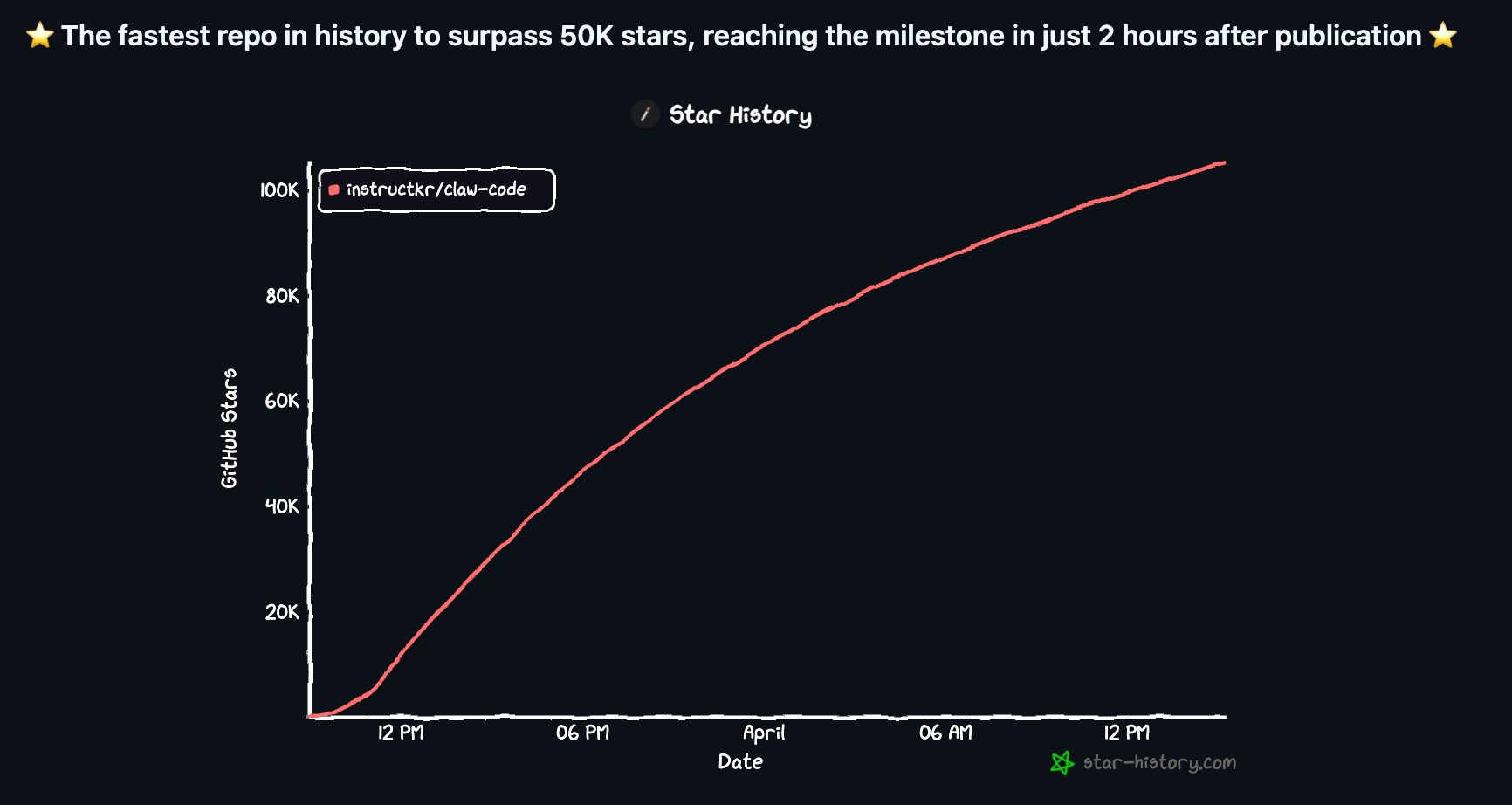
50,000 stars in about 2 hours. It hit 100K within a day.
ccunpacked.dev: The Architecture Explorer
Zakaria O.I.A. (@zackautocracy) built ccunpacked.dev — an interactive visual guide that maps Claude Code's internals: the agent loop, 50+ tools, multi-agent orchestration, and some unreleased features like an autonomous agent mode called "KAIROS."
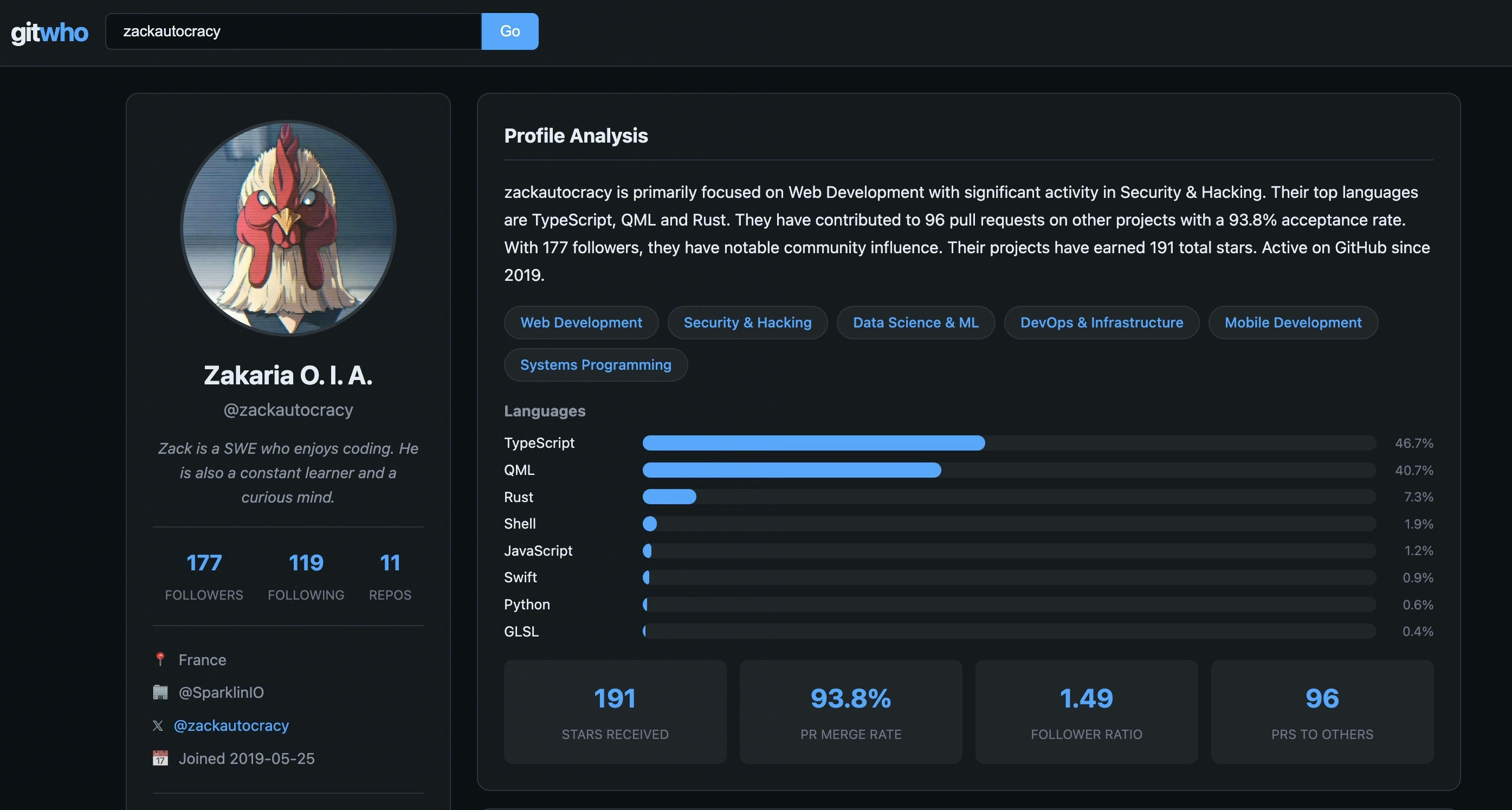
gitwho profile of @zackautocracy — sholuv.net/gitwho
If you're building with Claude Code and want to understand what's happening behind the scenes, it's worth a look.
The DMCA Fiasco
Anthropic's next move made things worse. They filed a DMCA takedown notice on GitHub — but due to how GitHub's fork network works, a single notice accidentally disabled 8,100+ repositories, including legitimate forks of Anthropic's own public Claude Code repo.
Boris Cherny, Anthropic's head of Claude Code, called the mass takedown accidental. Anthropic retracted most of the notices, limiting takedowns to one repository and 96 forks that actually contained the leaked source. GitHub restored access to the rest.
The Streisand Effect was in full force — the DMCA attempt drew even more attention to the leak than the leak itself. This video covers the DMCA fallout well.
Then Came the Malware
Within 24 hours of the leak making headlines, a different kind of repo started appearing — and these weren't built by curious developers.
Threat actors spun up fake GitHub repositories claiming to host the leaked Claude Code source, optimized them for search engines, and watched them climb to the top of Google results for queries like "leaked Claude Code" and "Claude Code download." Zscaler's ThreatLabz caught it first.
How the trap worked:
The repos looked convincing — clean READMEs promising "unlocked enterprise features" and "no message limits," with a .7z archive in the GitHub Releases section labeled "Claude Code - Leaked Source Code." Inside was a file called ClaudeCode_x64.exe.
How we know it was malware:
The .exe was a Rust-compiled dropper. On execution it deployed two payloads:
- Vidar v18.7 — an infostealer that siphons browser credentials, saved passwords, credit card data, crypto wallets, and session cookies, then exfiltrates everything to a C2 server
- GhostSocks — a SOCKS5 proxy backdoor that turns infected machines into relay nodes, letting attackers route their traffic through your computer
The red flags researchers spotted:
- The repo was run by account "idbzoomh" — a throwaway account with no history
- A second identical repo appeared under account "my3jie" — same code, same payload, same actor
- The archive was updated in short intervals, swapping in fresh payloads to evade signature detection
- One version included a fake "Download ZIP" button embedded as an image — not a real GitHub button, just a clickable image linking to the malicious archive
- No actual TypeScript source code in the repo, just the dropper
According to Trend Micro's analysis, this wasn't even a one-off. The Claude Code bait was part of a rotating lure operation active since February 2026, impersonating 25+ software brands while delivering the same Rust-compiled infostealer payload. Claude Code was just the flavor of the week.
The lesson: when something big leaks, the most dangerous repos aren't the ones with the leaked code — they're the ones pretending to have it.
Are You Shipping Source Maps?
This is not an Anthropic-only problem. Any project that compiles TypeScript, uses Webpack, Vite, or any bundler can make this exact mistake. One missed .npmignore rule, one wrong tsconfig.json setting, and your private source is public.
So I built srcleaks — a CLI tool that scans npm packages and live websites for accidentally shipped source maps.
# Install
go install github.com/sho-luv/srcleaks@latest
# Scan npm packages
srcleaks @anthropic-ai/claude-code react express
# Scan a live website
srcleaks https://example.com
# Scan all packages from an npm org
srcleaks --org anthropic-ai
It auto-detects whether you give it a package name or URL, checks for .map files, and reports one of three statuses: EXPOSED (source map found on a proprietary package), LEAK (map contains recoverable source code), or CLEAN. Open source packages are automatically marked clean — shipping source maps isn't a leak if your code is already public.
Use --proof to see the actual recovered source code as evidence.

The Takeaway
- What happened: Anthropic shipped a 59.8 MB TypeScript source map in their npm package by accident — reportedly for the second time
- Who found it: @Fried_rice (Chaofan Shou, Solayer Labs intern)
- What it exposed: ~512,000 lines of Claude Code's internal source (not customer data, not model weights)
- What the community built: claw-code (100K+ stars in a day), ccunpacked.dev (architecture explorer)
- The DMCA backfire: Anthropic accidentally took down 8,100+ repos, then retracted
- Why it matters: This is a packaging mistake anyone can make — and most teams don't check for it
- What to do: Audit your npm packages with srcleaks, or manually run
npm pack --dry-runand look for.mapfiles. Check your.npmignoreandtsconfig.json. Don't ship your decoder ring.